DAY 14 – Amazon Macie – Security & Compliance – Day Fourteen
Tweet This Blog – 100 days of Cloud on GitHub – Read On iCTPro.co.nz
- Data on 123 Million US Households Exposed Due to Misconfigured AWS S3 Bucket – TrendMicro
- Insecure Amazon S3 bucket exposed personal data on 500,000 Ghanaian graduates – Portswigger
- Leaky Buckets: 10 Worst Amazon S3 Breaches – Bitdefender
Some of the biggest leaks in recent years , the main reason for the hacks was misconfigured S3 Buckets. The best way to avoid your misconfiguration is to have proper monitoring and logging which is already provided by AWS.
👮 Policing your S3 infrastructure


 Amazon Web Services@awscloud
Amazon Web Services@awscloud

Amazon Macie uses machine learning to automatically discover, classify, & protect sensitive data in AWS: amzn.to/2wNnGR523:17 PM – 28 Aug 2017



.
A compliance and security service to automatically detect your unsecured data.
Amazon Macie gives you an monitoring , alerting and protection of your S3 buckets. This tool will audit S3 buckets to find –
- Discover your sensitive data at scale
- Continual evaluation of your Amazon S3 environment
- Scalable on-demand and automated sensitive data discovery jobs
- Fully managed sensitive data types.
- Custom-defined sensitive data types.
- Multi-account support and integration with AWS organizations
- ML/Ai helps to finds access pattern.
- Assign business values in the form of risk score.
- PII/PHI data protection.
- Alert on unauthorized ACL changes.
- Maintain Compliance requirement (GDPR).
Check out this link to understand the availability for your regions.
Macie helps to get alerts on Anonymized access , config compliance, credential loss, data compliance (PII,PHI), file hosting(malware detection), Identity Enumeration, information loss, location anomaly, open permissions, privileged escalation, Ransomware, Service disruption, suspicious access.
🛠️ Enable Amazon Macie
📘 Knowledge Requirement
- S3 buckets
- CloudTrail, enable CloudTrail
🤖 The Macie
- Goto your console and search for Amazon Macie
- now click Get Started

- click on the enable Macie

Thats it , now wait till Amazon Macie analyze your account.
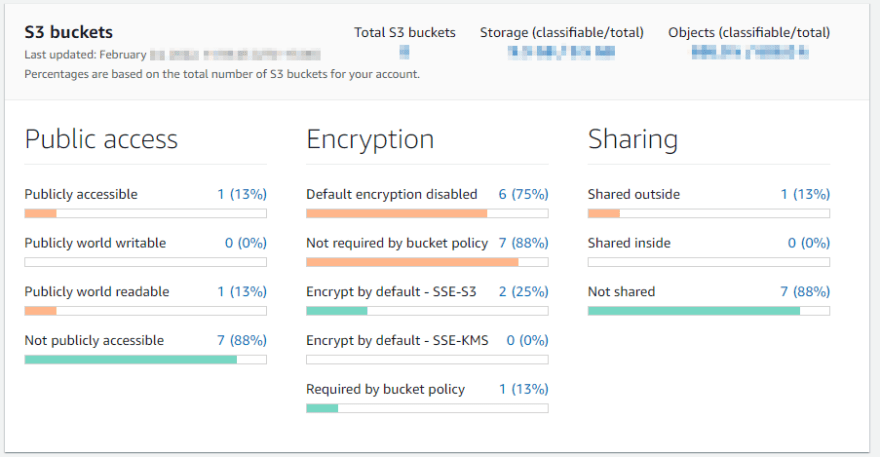
After few minutes it will give you a brief summery of your s3 buckets
🪣 Configure your bucket
Setup custom identifiers
Select Custom data identifiers and click create.
I am adding a custom data identifier for SIRET-NICs data. and click submit.
Configure a Job
Now lets configure a bucket for Amazon Macie to police.
- On dashboard click s3 buckets and select your buck and click Create Job.
- Refine your scope, for this demo purpose am keeping it as One-time job. Click Next

- Now select your Custom data identifier & Click Next.
- Give a Name and description & Click Next.
- review and click Submit.
if you want to store results for long term , consider Configuring an S3 bucket of your sensitive data discovery results. this can be done in Discovery results under Settings menu.
Overview of all buckets
- Select buckets from dashboard to see an overview
Publication of findings
Macie automatically publishes all new and updated findings to Amazon EventBridge. You can configure Macie to publish findings to additional destinations, and specify how often to publish updates to all destinations.

✅Connect with me on Twitter
🤝🏽Connect with me on Linkedin
🧑🏼🤝🧑🏻 Read more post on dev.to or iCTPro.co.nz
💻 Connect with me on GitHub